The following graph shows the rate of discovery of TrickBot versions in the wild, based on shared mcconfs. (Note: The flatter the line, the more frequently versions are discovered.)
Eleven new versions were discovered in the week commencing 19th February 2018 (A-1000131, A-1000132, A-1000133, B-1000052, B-1000054, B-1000055, B-1000056, B-1000057, B-1000058, B-1000059, and B-1000061), thirteen the week before, and nine the week before that. Three of the discovered versions extend the original iteration of version numbers (which I refer to as iteration A), taking this to 1000133. Eight shared versions extend the secondary botnet which is reusing earlier version numbers, taking them to 1000061. (I track these as part of a new, distinct iteration, iteration B, of the version numbers.)
The following graph shows the number of server entries using ports:
- 443 (HTTPS);
- 444 (Simple Network Paging Protocol);
- 445 (IBM AS Server Mapper) -- INACTIVE;
- 449 (Cray Network Semaphore Server); and
- 451 (SMB) -- INACTIVE.
The following map shows the geographical location of 71 (those with location data) of 74 (scanned by Shodan) of the 92 C2 servers used in the analysed configs.
According to Shodan's most recent data:
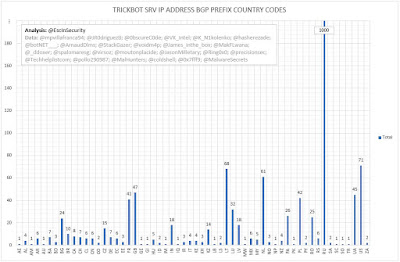
The following table shows the BGP allocations of C2 servers' IP addresses to country by TrickBot version.
According to Shodan's most recent data:
- 50 are running OpenSSH, 19 are running nginx, four are running Exim, three are running Apache, three are running Dropbear SSH, two are running Postfix, and one is running PostgreSQL.
Finally, the following table shows the top 25 BGP prefixes used by TrickBot for C2 servers.
Full size versions of the images included in this post are available here.
Thanks to @mpvillafranca94, @JR0driguezB, @0bscureC0de, @virsoz, @spalomaresg, @VK_Intel, @K_N1kolenko, @hasherezade, @botNET___, @ArnaudDlms, @StackGazer,@voidm4p, @James_inthe_box, @MakFLwana, @_ddoxer, @moutonplacide, @JasonMilletary,@Ring0x0, @precisionsec, @Techhelplistcom, @pollo290987, @MalHunters, @coldshell, @0x7fff9 and @MalwareSecrets for sharing the mcconfs.
Thanks to @mpvillafranca94, @JR0driguezB, @0bscureC0de, @virsoz, @spalomaresg, @VK_Intel, @K_N1kolenko, @hasherezade, @botNET___, @ArnaudDlms, @StackGazer,@voidm4p, @James_inthe_box, @MakFLwana, @_ddoxer, @moutonplacide, @JasonMilletary,@Ring0x0, @precisionsec, @Techhelplistcom, @pollo290987, @MalHunters, @coldshell, @0x7fff9 and @MalwareSecrets for sharing the mcconfs.